- Products & services Products & services
- Resources ResourcesLearning
- Learning
- Identity University Get technical training to ensure a successful implementation
- SailPoint professional certifications & credentials Advance your career or validate your identity security knowledge
- SailPoint recertification program Get recertified by demonstrating ongoing learning
- Training onboarding guide Make of the most of training with our step-by-step guide
- Training FAQs Find answers to common training questions
- Community Community
- Compass
- :
- Discuss
- :
- Community Wiki
- :
- IdentityIQ Wiki
- :
- Credential cycling for Privileged Access Management
- Article History
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Content to Moderator
Credential cycling for Privileged Access Management
Credential cycling for Privileged Access Management
Back to the IdentityIQ 7.3 overview: What's new in IdentityIQ 7.3
- Overview
- About credential cycling
- How credential cycling works in IdentityIQ
- Working with the credential configuration template
- Template general guidelines
- BeyondTrust
- CyberArk
- CyberArk vendor prerequisites
- How to generate a hash to add to the application if the SCIM server is not installed on the Identity...
- Working with the CyberArk template
- Direct attribute mapping
- Credential cycling in an application
- Additional information
Overview
IdentityIQ version 7.3 continues to build out a robust Privileged Access Management (PAM) solution, by adding credential cycling to IdentityIQ's support for PAM.
The Identity University eLearning course on IdentityIQ 7.3 New Features includes a detailed lesson on enabling credential cycling. The course is available in early September 2018.
Important: For the most up-to-date information about configuring and using the PAM module, refer to the IdentityIQ product documentation on PAM.
About credential cycling
At a high level, credential cycling is a feature that allows applications which require credentials (such as username and password) to obtain that information directly from a PAM source, such as a CyberArk or Beyond Trust solution. Previously, these credentials had to be set up in the application definition manually, and if any information changed in the PAM solution, those changes had to be made manually in IdentityIQ by an administrator. With IdentityIQ 7.3, the credential cycling feature lets credentials be pulled directly from the PAM vault at runtime, with no manual intervention (other than initial configuration) by the IdentityIQ administrator, adding both security and convenience.
How credential cycling works in IdentityIQ
With version 7.3, you can manage credentials solely within your PAM solution. Essentially, an administrator defines which applications will use credential cycling, which PAM solution provides those credentials, and how each of the applications will contact the PAM vault to retrieve the credentials. This is done via a configuration file that is imported into IdentityIQ as an object.
Here is a brief summary of how credential cycling is configured in IdentityIQ. A more detailed look at the template and the configuration options is provided in a later section.
- Your applications should already be set up in IdentityIQ (Applications > Application Definition)
- In some cases the discovery options in an application can be disabled when credential cycling is enabled, so perform any necessary discovery operations before enabling credential cycling for the application.
- A template file is provided in your IdentityIQ installation, which you use as a model for setting up your own configuration. The template file is
[IdentityIQ installation directory]\WEB-INF\config\credentialConfigurationTemplate.xml
- You edit this file to define your PAM source values. The template includes models for BeyondTrust and CyberArk, as well as a solution-neutral direct attribute mapping option.
- You also include information in the file about which of your applications in IdentityIQ will use credential cycling, and how the PAM-provided values map to your application fields for authentication.
- You import the edited XML file into IdentityIQ (using gear > Global Configuration > Import File)
- Importing the file creates a new object in IdentityIQ: Credential Configuration
- If you need to update your credential cycling configuration, you can modify and re-import the credential configuration XML. You can also edit the Credential Configuration object directly in the Debug pages.
Working with the credential configuration template
The credentialConfigurationTemplate.xml is located in the WEB-INF\config directory of your IdentityIQ installation.
The template file includes sections for BeyondTrust, CyberArk, and a solution-neutral direct attribute mapping option. If you are using a PAM solution other than BeyondTrust or CyberArk, you can use those sections of the template as a model for configuring another PAM solution.The file is fully commented, to provide guidance as you insert your configuration settings.
Template general guidelines
- Remove the sections that you will not use before importing the template. For example, if you want to implement just a CyberArk solution, remove the template sections for BeyondTrust and the direct mapping option.
- Each solution option has a section for mapping Credential Source details, which manage the connection to your PAM solution, and a Credential Association section, which handles the association of the secure credentials in your PAM solution to your applications in IdentityIQ.
- As always when working with templates, the best practice is to make a copy of this template to hold your specific configuration values, rather than modifying the original template file.
BeyondTrust
Here are some key points to observe when you work with the BeyondTrust portion of the template:
Note that to enable credential cycling with the BeyondTrust PowerBroker Password Safe application, passwords must be configured in the JSON format. For example:
{"bt_user":"MyUserName","bt_password":"MyPasswordValue"}
In the Credential Source section, you configure
- The URL to your BeyondTrust source
- The "run as" user for authenticating to your source
- An API key for authentication
- Your BeyondTrust Managed System and Managed Account names. In the Credential Source section, you set overall values for your overall BeyondTrust implementation. If specific applications will use different or unique Managed Systems or Managed Accounts, you can set values for those that are specific to particular applications in the Credential Association section.
In the Credential Association section, you configure
- The name(s) of your IdentityIQ applications that will use credential cycling
- The attributes for your application's username, and the corresponding BeyondTrust username that provides the secure username credential to the application at runtime.
- Any application-specific overrides to the overall BeyondTrust Managed System or Managed Account names
<CredentialSource credentialClass="sailpoint.pam.credential.BeyondTrustCredentialManager" name="beyondTrust ">
<!-- The attributes in this map are used mainly to communicate with BeyondTrust.
Any values here can be overridden by values of the same name in the attributes
map of each credential association. Required attributes must either be configured
here or in every credential source. Attributes:
Required: url
Required: runas
Required: apikey
Required: managedSystemName
Required: managedAccountName
Optional: durationMinutes
Optional: credentialCacheMinutes
Optional: checkInReason
Optional: checkOutReason
-->
<Attributes>
<Map>
<entry key="url">
<value><String>https://your.beyondtrust.server/BeyondTrust/api/public/v3/</String></value>
</entry>
<entry key="runas">
<value><String>runas_user</String></value>
</entry>
<entry key="apikey">
<value><String>your_BeyondTrust_api_key_goes_here</String></value>
</entry>
<entry key="managedAccountName" value="beyond_trust_managed_account_name"/>
<entry key="managedSystemName" value="beyond_trust_managed_system_name"/>
</Map>
</Attributes>
<!-- ***Application Configuration -->
<CredentialAssociation applicationName="application_name"
attributeName="application_username_attribute"
credentialAttributeName="bt_user">
<!-- *** Attribute values go here. These attributes can be used to override values from
*** above, or can be left out if not needed -->
<Attributes>
<Map>
<entry key="managedAccountName" value="special_beyond_trust_managed_account_name"/>
</Map>
</Attributes>
</CredentialAssociation>
<CredentialAssociation applicationName="application_name"
attributeName="application_password_attribute"
credentialAttributeName="bt_password"/>
</CredentialSource>
CyberArk
CyberArk vendor prerequisites
CyberArk implementations require the installation of CyberArk’s Credential Provider API. The Credential Provider API enables passwords that are stored in CyberArk Digital Vaults to be retrieved by IdentityIQ. This API must be installed on the same server IdentityIQ is installed on.
Note that the Credential Provider API is NOT the same as CyberArk’s Central Credential Provider, which provides access to the Digital Vault via web services. For full details on how to obtain and use the Credential Provider API, please refer to CyberArk’s documentation.
IdentityIQ uses the “Application Hash Value” method of authenticating to the API; other methods of authentication will not work. Verify connectivity to the CyberArk Digital Vault using the command line clipasswordsdk before attempting to construct the attributes of the Credential Cycling Configuration object.
- Note: For CyberArk integrations, IdentityIQ version 8.3 and later requires version 9.8 of the CyberArk components. CyberArk customers should confirm the appropriate version of the library for their version of CyberArk, and obtain it from the vendor if necessary.
How to generate a hash to add to the application if the SCIM server is not installed on the IdentityIQ server:
Note: For more information, refer to CyberArk’s Credential Provider and ASCP Implementation Guide.
First, ensure that you have extracted the pam-credential.jar file from the identityiq.war. If you have deployed IdentityIQ using the "exploded" form of the war file, you don't need to take any extra steps to extract the pam-credential.jar file; however, if you are not using this deployment strategy, you will have to extract the pam-credential.jar from the identityiq.war file, perform the steps below, then repackage the pam-credential.jar back into the identityiq.war file.
- Run the CyberArk utility 'JavaAIMGetAppInfo' (under \CyberArk\ApplicationPasswordProvider\Utils):
(Unix) java -jar javaaimgetappinfo.jar GetHash -AppExecutablesPattern=/{path to identityiq directory}/WEB-INF/lib/pam-credential.jar
(Windows) java -jar JavaAIMGetAppInfo.jar GetHash /AppExecutablesPattern=C:\{path to identityiq directory}\WEB-INF\lib\pam-credential.jar - Copy the generated hash to the vault:
- log in to the CyberArk Web Application
- Applications > SailpointIIQ > Authentication > Add Hash
- Wait approximately 3 minutes, to allow the ‘privileged session manager’ to read the new configuration, or restart the CyberArk Privileged Session Managers service for the configuration change to take place immediately.
Working with the CyberArk template
Here are some key points to observe when you work with the CyberArk portion of the template.
In the Credential Source section, you configure
- The name of your CyberArk safe - this information comes from CyberArk.
- The folder where your secure credentials are stored. Use "root" here if you do not use folders.
- An AppID, which is a unique identifier, used for authorization, which the CyberArk Credential Provider creates when it’s installed on a host
In the Credential Association section, you configure
- The name(s) of your IdentityIQ applications that will use credential cycling
- The attributes for your application's username, and the corresponding CyberArk username that provides the secure username credential to the application at runtime.
- A CyberArk object, which is CyberArk's representation of a collection of attributes which store password and user name information
- Any application-specific overrides to the overall CyberArk settings
<CredentialSource credentialClass="sailpoint.pam.credential.CyberArkCredentialManager" name="cyberark">
<!-- The attributes in this map are used mainly to communicate with CyberArk.
Any values here can be overriden by values of the same name in the attributes
map of each credential association. Required attributes must either be configured
here or in every credential source. Attributes:
Required: safe
Required: folder
Required: appId
Required: object
-->
<Attributes>
<Map>
<entry key="safe" value="cyber_ark_safe_name"/>
<entry key="folder" value="cyber_ark_folder_name"/>
<entry key="appId" value="cyber_ark_app_ID"/>
</Map>
</Attributes>
<!-- *** Application Configuration -->
<CredentialAssociation applicationName="application_name"
attributeName="application_username_attribute"
credentialAttributeName="CyberArk_username_attribute">
<!-- *** Attribute values go here. These attributes can be used to override values from
*** above, or can be left out if not needed -->
<Attributes>
<Map>
<entry key="object" value="object_value"/>
</Map>
</Attributes>
</CredentialAssociation>
</CredentialSource>
Direct attribute mapping
Here are some key points to observe when you work with the mapping portion of the template:
In the Credential Source section, you configure your actual credential values, since you are not connecting to a third-party PAM source. It is a good practice to use encrypted passwords in this section.
The Credential Associations settings connect the values in the Credential Source section to your applications as shown in the template XML below.
<CredentialSource credentialClass="sailpoint.pam.credential.MapCredentialManager" name="mapCredManager">
<!-- The attributes in this map are the values that will be returned by the map credential manager.
It's probably a good idea to encrypt these so they are not stored in plain text if the values
are sensitive -->
<Attributes>
<Map>
<entry key="credentialValues">
<value>
<Map>
<entry key="map_username_attribute" value="john_doe_username"/>
<entry key="map_password_attribute" value="super_secret_password"/>
</Map>
</value>
</entry>
</Map>
</Attributes>
<!-- *** Application Configuration -->
<CredentialAssociation applicationName="application_name"
attributeName="application_username_attribute"
credentialAttributeName="map_username_attribute"/>
<CredentialAssociation applicationName="application_name"
attributeName="application_password_attribute"
credentialAttributeName="map_password_attribute"/>
</CredentialSource>
Credential cycling in an application
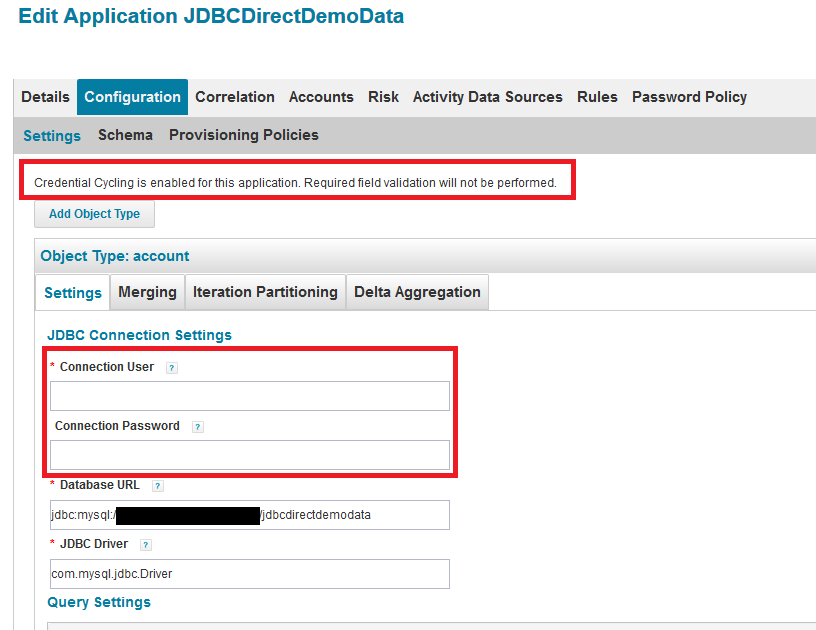
When credential cycling is configured for an application, the Application Definition UI shows a message to indicate this. Although the relevant credential fields (in this example, Connection User and Connection Password) are still marked as requiring values, these fields are not validated when credential cycling is enabled, and so can be left blank, or can include dummy values.
Additional information
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Content to Moderator
Is there a way to fetch a password from a rule? We have few rules that query AD before provisioning an account using hardcoded encrypted password. How do we fetch AD password from the CyberArk vault from such rules? Thank you in advance.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Content to Moderator
Regarding licensing: In case anyone hits this article in the future ---
It requires both a SailPoint PAM license as sachinc1 mentioned, and *also* will consume one CP Agent License per installed SailPoint server on the CyberArk side.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Content to Moderator
Hi All,
We have enabled the credential cycling for an app but we also use target source config with same credential.
Can someone suggest how can we enable the Credential cycling for the Target Source?
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Content to Moderator
Hi All,
I am Trying to Retrieve Password for Active Directory Application, I am able to get the password from CyberArk for Domain and Forest User, but i am unable to get the password for IQService Credentials.
Below is the Snippet :
<CredentialAssociation applicationName="Test-AD1" attributeName="IQServiceConfiguration[IQServiceUser='Domain\\USER'].IQServicePassword" credentialAttributeName="Password">
<Attributes>
<Map>
<entry key="object" value="VALUE"/>
</Map>
</Attributes>
</CredentialAssociation>
Can someone let me know if you are able to retrieve the password for IQService as well.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Content to Moderator
@sathish-nallathambi Looks like you are giving the incorrect values in the credential configuration refer below and update the value from your configuration, along with the below you need to see if your CredentialSource configuration is correct in credential config file.
<CredentialAssociation applicationName="Test-AD1" attributeName="forestSettings[user='Domain\\User'].password" credentialAttributeName="Password">
<Attributes>
<Map>
<entry key="object" value="Value of the name attribute from CyberArk"/>
</Map>
</Attributes>
</CredentialAssociation>
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Content to Moderator
@sachinc1 Thanks for your response, I dont have any issues in retrieving password for Domain and Forest users. I am trying to retrieve password for IQService, and thats were i am facing issue. The response you shared above is for Forest and i do not have any issues in Pulling forest password.
Could you please let me know if you are able to pull IQservice password.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Content to Moderator
BeyondTrust guide is much better than the IIQ guide here. Here is a sample
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Content to Moderator
Hello All, Thanks for the above documentation which was really helpful on credential cycling configuration. I need one help, did anyone know, how to write a format/syntax in CredentialConfiguration.xml for AD with multi domain settings.
Can someone help me with this.
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Content to Moderator
@Saraf , this link has documentation specific to AD configuration.
https://documentation.sailpoint.com/identityiq/help/pam/cyberarkconfiguration.html
I've not used this myself yet, but plan to early next year. Their example...
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Content to Moderator
Hello All,
Does anyone know when the CredentialConfiguration configuration is called to retrieve the current password of the application?
Or did I completely misunderstood this feature?

