- Products & services Products & services
- Resources ResourcesLearning
- Learning
- Identity University Get technical training to ensure a successful implementation
- SailPoint professional certifications & credentials Advance your career or validate your identity security knowledge
- SailPoint recertification program Get recertified by demonstrating ongoing learning
- Training onboarding guide Make of the most of training with our step-by-step guide
- Training FAQs Find answers to common training questions
- Community Community
- Compass
- :
- Discuss
- :
- Community Wiki
- :
- IdentityIQ Wiki
- :
- Password Interceptor - Client installation and uninstallation
- Article History
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Content to Moderator
Password Interceptor - Client installation and uninstallation
Password Interceptor - Client installation and uninstallation
- Overview
- Uninstalling Password Interceptor (if you had it installed and it isn’t working or we don’t know, so...
- Fresh installation on DC (considering it as primary server)
- Verification: How to check if this is installed successfully
- Installation on Secondary servers
- Automated Installation in Secondary DC using BSA tool
- Pre-requisites
- Capabilities needed at IIQ side for Password Interceptor to work
- TLS Support
- useSiteSpecificEncryptionKey /ADKeys.xml
- Update loggers for testing/enable debug default it is 0
- How PWI Client works
- Troubleshooting steps
- Additional reference
Overview
The Password Interceptor will intercept the Passwords from AD Domain Controller and pass it to IIQ to enabling Password Sync with other systems like OUD/Directory System.
Installation has to be done differently in Primary and Secondary DCs. Primary domain controller is always the first domain controller the password interceptor is manually installed. Secondary domain controllers are the remaining domain controllers where the configuration and keys are replicated, in addition to the installation
Please go to the Compass link below for more details.
Uninstalling Password Interceptor (if you had it installed and it isn’t working or we don’t know, so check it first and clean)
Uninstallation of Password Interceptor Client can be performed using one of the following methods:
- Using MSI: Execute the .msi file to uninstall the service or double click on the .msi file for the uninstall option to appear.
- Using the Command Line: Run the following command to uninstall the Password Interceptor Client silently:
- (For 32-bit) msiexec /x "SailPoint Active Directory Password Interceptor-X86.msi " /qn
- (For 64-bit) msiexec /x "SailPoint Active Directory Password Interceptor-X64.msi " /q
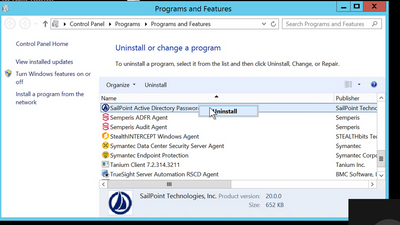
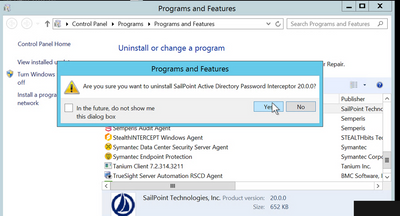
3. Using the Programs and Features Console:
- Login to Each DCs , Open Control Panel and navigate to Programs and Features.
- Select SailPoint Active Directory Password Interceptor 20.0.0 and click Uninstall.
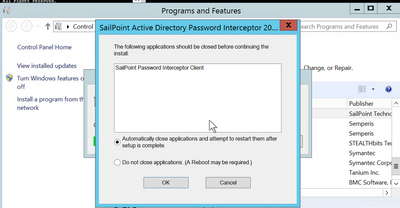
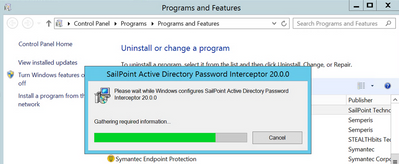
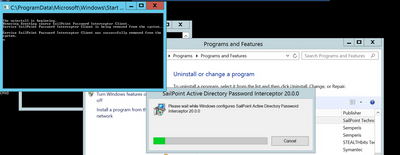
3. Restart the Server
Verification of Uninstallation
Note: PowerShell script has all checks as part of prerequisite.
Fresh installation on DC (considering it as primary server)
- Extract SailPoint Active Directory Password Interceptor-20.0.0.zip to a directory.
- Depending on the operating system navigate to the following appropriate directory and run SailPoint Active Directory Password Interceptor.msi or setup.exe:
- (For 32-bit): pathOfPasswordInterceptor\x86\SailPoint Active Directory Password Interceptor-X86.msi
- (For 64-bit): pathOfPasswordInterceptor\x64\SailPoint Active Directory Password Interceptor-X64.msi
Where pathOfPasswordInterceptor is the path where .zip file is unzipped in step 1 above. - On the Welcome dialog box, click Next to continue the installation.
- On the License Agreement dialog box, select I Agree and click Next.
- Select the directory for the installation and click Next.
(default location: C:\ProgramFiles)
- Fill in the configuration information and click Next.
- Make sure for first installation you select initial
- For additional encryption please select useSiteSpecificEncryptionKey
Add below config details (Mandatory Parameters)
- application name
- User
- Password
- url
- OU Path
Optional parameters:
- Enter the optional additional configuration parameters click Next:
- Scope
- Search filters
- Click Next to proceed.
The screen shows the confirm installation page.
- On the Installation Complete dialog box click Close to exit.
- Reboot server
Verification: How to check if this is installed successfully
- Successful installation will have Windows Service named “SailPoint Password Interceptor Client” , check if the service is available.
- dll with name SAILPOINTPWDINT.dll in system32 folder should be available
- It would also create a OU named PWDINT_SERVER_OU in DC=ABC,DC=DEF. The ServiceConnectionPoint object name HOST_ADDR_<Hostname/IPAddressfrom url> would be created within the PWDINT_SERVER_OU.
- This object would hold the connection details, application name and other details provided in the above config entries.
- The object contains accesstoken1 , accesstoken2
These access tokens represent encrypted form of "user:password". There is a length restriction in SCP keywords, hence we split in multiple tokens. Also, first we encrypt credential using a 256 bit symmetric key using aes-256-cbc, and then that symmetric key is encrypted with RSA key. And then these two cipher texts are stored in these tokens in scp object.
Installation on Secondary servers
- For Subsequent Installations on Additional Domain Controllers:
- For upgrading to SailPoint Active Directory Password Interceptor version 20.0.0 from 7.1/7.2 for subsequent installations on additional domain Controllers, perform the uninstallation steps as mentioned above (up-to step 5).
- For installation, provide the value of OUPath (Password Interceptor for Microsoft Active Directory configuration OU).
OUPath must be the same as provided during initial installation.
NOTE: On Installation Parameters screen, do not select the Initial Setup option. - Reboot the system.
Above is manual installation , for automated one , please follow below step
Automated Installation in Secondary DC using BSA tool
Pre-requisites
The Servers on which the installation needs to be done, should be up and running.
The implementer account (used in BSA tool) used for installing PWI should have required rights, AD Directory access, Registry Editor access and Windows Service access.
BSA job should be created with below steps.
step 1 for pre requisite check using PowerShell script (write script to check prerequisite)
Step 2 installation of PWI using VB script/package. (script needs to be created)
Step 3 Reboot server.
Step 4 Copy ADKeys.xml from primary server
Step 5 Script run to import key file with restart of services.
Based on domain packages should be created and placed on server. Each domain has different OU’s (example : DC=zone1, DC=zone2, DC=zone3)
DC=SailPoint, should be used for Prod and for dev DC=SailPointDev
Note: If there is already any Machine keys file available or any registry available, that should be removed through PowerShell script (step 3.a).
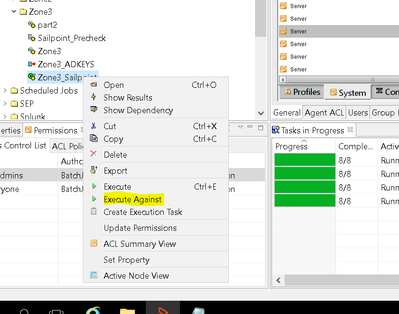
Login to the BSA tool and navigate to the path where installation script is : [/BladeLogic/Jobs/Software_Repository/SailPoint/<domain>/<domain script>] for <domain> and click on Execute Against.
Sample :
Capabilities needed at IIQ side for Password Interceptor to work
WebServicesExecutor” capability is the only privilege that an account needs, in order to invoke the PWI rest service at IIQ/Onecert side
TLS Support
Password Interceptor for Microsoft Active Directory now communicates to IdentityIQ server using version 1.2 of TLS protocol, by default .Net 4.5 and above.
- Windows server 2008 doesn’t support TLS 1.2 , it supports TLS 1.0
useSiteSpecificEncryptionKey /ADKeys.xml
Q: When file is created and how?
ADKeys.xml is a RSA key container, created when we run
PwdClient.exe –exportKeys command.
- This will be created only when PWI is installed with useSiteSpecificEncryptionKey option.
- ON first installation of PWI in a domain, these site specific keys are generated on that DC. For rest of the DCs
Secondary) in that domain, keys are required to exported from first DC and imported on rest of them.
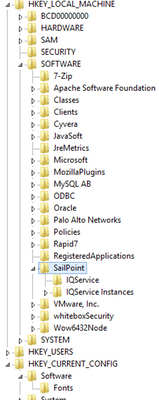
- Note: If there is already any Machine keys file available or any registry available, that should be removed first. Path to registry is as follows :
Q: What are the implications of using site specific encryption?
- UseSiteSepcificEncryptionKey option enables use of cryptographic keys specific to that installation, whereas the standard key is the default one comes with the PWI.
- Use site specific encryption option uses hybrid encryption mechanism to encrypt IIQ credentials (username and password).
- First encrypt IIQ credentials through AES encryption using key generated at run time. Then encrypts AES key itself through RSA. Then append encrypted symmetric key to encrypted IIQ credentials and store in the AD.
- So basically it encrypts and decrypts IIQ creds.
Update loggers for testing/enable debug default it is 0
- To update log level: PwdClient.exe –l "3"
- Log File path :
Default: Password Interceptor Client Home folder
For example, -f "C:\Program Files\SailPoint\ADPwdClient"
How PWI Client works
AD to IdentityIQ --> Password interceptor client for AD picks up new password, sends it to IdentityIQ and IdentityIQ starts a workflow to distribute it to other systems.
The password interception happens immediately, unless some network issues are there, or IdentityIQ is unreachable. In that case, the intercepted password is kept by the PWI client, which will retry a number of times to deliver it to IdentityIQ. It stays in queue for 24 hours (by default and can be edited).
The following points describe the sequence of events triggered when an Active Directory user changes password:
- A user requests a Password change on a workstation which belongs to one Domain Controller (DC) in the Domain.
- On the Domain Controller (DC), the Local Security Authority (LSA) calls the password filter that is registered on the computer.
Password filters provide means to implement password policy and change notifications. When a user makes a password change request on a Domain Controller, the Local Security Authority (LSA) calls the password filters registered on the system.
NOTE:
Password Interceptor must be installed on every Domain Controller (that's where the LSA service runs and detects password change request for Active Directory).
Password Interceptor monitors LSA service to intercept password.
The DC is the only place where password can be captured in clear text.
- The Password Change request is written to the Password Interceptor Client which is a Windows service running on the same computer.
- The intercepted messages containing the password data from the Password Interceptor Client are sent to the server.
- The connection details of the Server, including the host name and port are stored in an Active Directory object of serviceConnectionPoint class. It is stored in Organisational Unit object and named as PWDINT_SERVER_OU.
Troubleshooting steps
- Make sure the user used for installation has OU creation permission on DC
- If the site scripting key is not used , FipsAlgorithmPolicy must be disabled, can be updated in registry:
HKLM\System\CurrentControlSet\Control\Lsa\FIPSAlgorithmPolicy\
- Check permissions on RSA/MachineKeys folder , system user should have full permissions.
C:\ProgramData\Microsoft\Crypto\RSA\MachineKeys.
- Manually change the password using command :
PwiClient.exe -user “<username>” -password “<password>”
- Loggers to be enabled while debugging:
- log4j.logger.sailpoint.rest.PasswordInterceptResource=all
log4j.logger.sailpoint.api.IdentityLifecycler=all
Additional reference
- https://community.sailpoint.com/t5/IdentityIQ-Forum/quot-WebException-raised-The-remote-server-retur...
- https://community.sailpoint.com/t5/IdentityIQ-Forum/What-admin-access-is-needed-to-run-Password-Inte...
- https://community.sailpoint.com/t5/IdentityIQ-Forum/Password-Sync-Issues-Using-Password-Interceptor-...
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Content to Moderator
Any command to check the latest version of password interceptor in our AD or DC?

